Experts in Internet of Things and Operational Technology penetration testing
Train with us to develop your IoT and OT hacking skills. Work with us to strengthen your IoT and OT defences.
Train with us to develop your IoT and OT hacking skills. Work with us to strengthen your IoT and OT defences.

At You Gotta Hack That, we are dedicated to securing the future by mastering the present. That sounds very grandiose but that is how we see things.
We specialise in Internet of Things (IoT) and Operational Technology (OT) penetration testing, as well as delivering advanced technical offensive security training courses. We find this fun and interesting, you find this deeply assuring.
In any case, we are committed to empowering organisations like yours to protect their most critical assets.

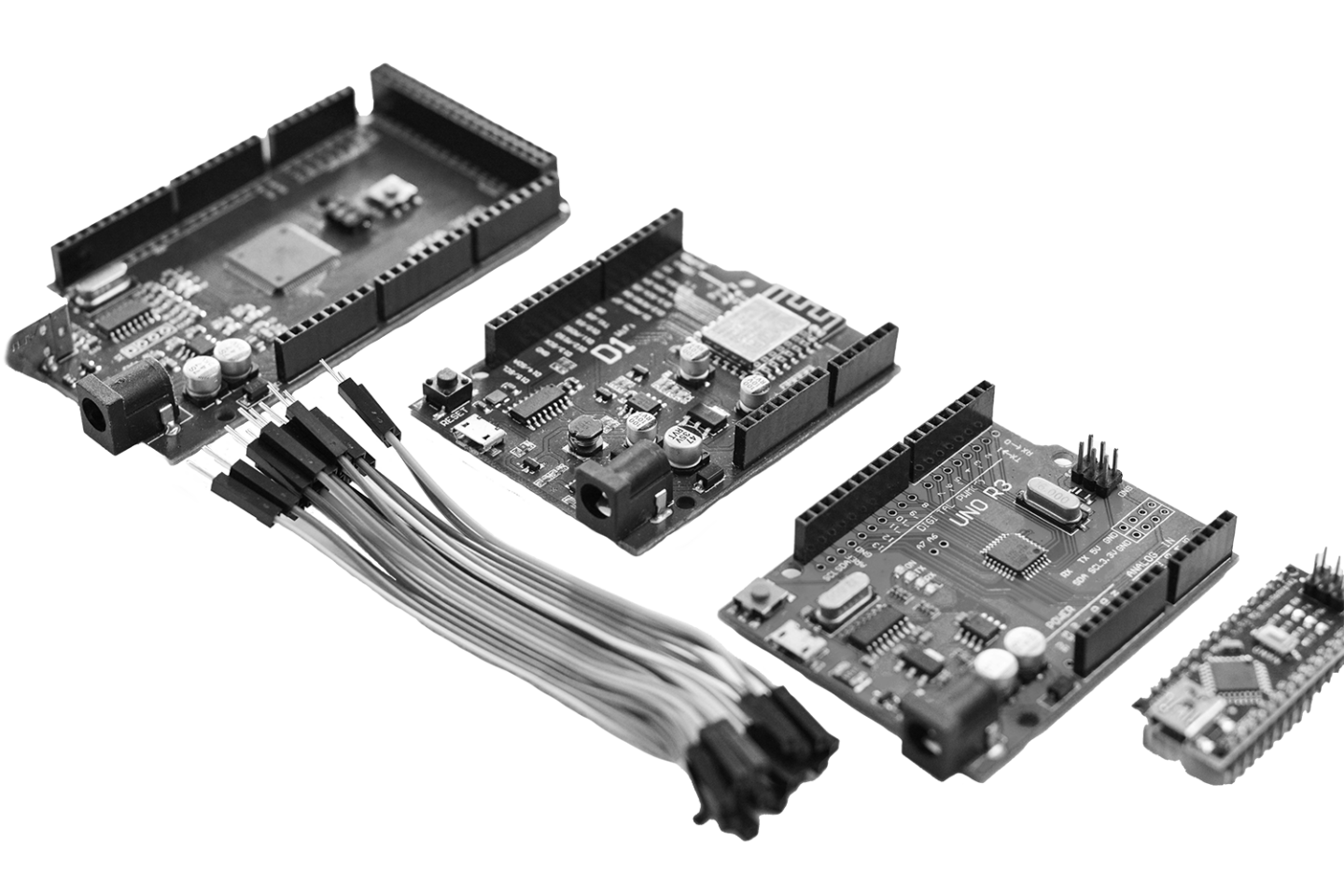
At You Gotta Hack That, we offer advanced technical training. These course modules are new and have been launched because no other course like it exists.
Each module is specifically designed to empower cybersecurity professionals dealing with IoT and OT assurance challenges. When you complete our course, you will have with the specialised skills needed to understand the security of an IoT or OT environment.
Our courses are crafted by leading experts who bring extensive hands-on experience and a deep understanding of the unique complexity within these domains. Whether you’re looking to enhance your foundational knowledge or master advanced techniques, our training programs deliver the practical expertise required to excel in the field.

At You Gotta Hack That, we provide specialised IoT and OT penetration testing services. Far too often we have conversations that quickly identify that an environment might well have been pen testing, but, it it was performed with an IT mindset.
This means that the methodology and toolchain used might not give much assurance within an OT or IoT problem space. Our services are designed to assess your critical system’s defences and takes into account the different technological space you are working in.
Our expert team tailors IoT and OT penetration tests based on our conversations with you, making sure that your security assessments meet the unique context of your architecture, infrastructure, devices, and networks.